In the modern era of digital communication, phishing is a scam that many individuals have seen hit their inboxes time and time again. And while businesses may have preventive plans in place to reduce the risks associated with phishing emails, mitigating the attack ultimately lies on the keen senses of those opening suspicious emails.
Training employees on the tell-tale signs of a phishing email isn’t a one-time deal. Cybercriminal groups are creative, continuously altering phishing campaigns to align with current events. So, as you can imagine, the uncertainty surrounding the on-going pandemic offered opportunity for many criminals to capitalize on the concerns of curious individuals. In particular, recent phishing attacks have focused on three major topics: the spread of COVID-19, the status of stimulus checks, and the reopening of the economy.
What is Phishing?
Before we dive deeper into how phishing has taken on a whole new persona in the early months of 2020, let’s first explore what these schemes entail. In its most basic form, phishing is a confidence scam, usually over email, where an attacker pretends to be a reputable authority. In turn, recipients of these emails feel confident completing the action asked of them; such as clicking a link, downloading a file, or completing a financial transaction.
Regardless of the action requested, phishing emails appear legitimate; sometimes even using the language and imagery found in standard communication from the person or organization from which the email appears to be from. In turn, individuals feel comfortable completing the request and ultimately compromising critical information.
Did COVID-19 Increase Phishing Scams?
While the risks associated with phishing attacks have remained high for some time, the recent pandemic has brought about new concerns for those businesses allowing employees to work remotely. Since March, researchers at Reuters have reported that government agencies, Google, and many cybersecurity-based firms have been recording an increase in coronavirus-based attacks; specifically designed to lure individuals distracted by the events taking place around them.
For many employees, security isn’t at the forefront of their minds. Instead, they’re understandably focused on meeting their bottom line, helping children with school-work, attending digital meetings, and learning how to navigate a virtualized workspace filled with new applications and updated processes. As mentioned previously, cybercriminals understand that this transition offers an opportunity to attack; with many recent phishing emails targeting those individuals that are new to the remote working lifestyle.
Take, for example, recent phishing emails attempting to mimic meeting invitations from the popular web-conferencing platform known as Zoom. Originally reported by Sophos Labs, scammers are distributing emails appearing to be from executive team members within organizations; demanding that employees join immediately to ensure the security of their jobs. Upon clicking the provided Zoom meeting link, individuals are sent to a pixel perfect login page where scammers can collect the account credentials the individual enters.
Noting that these threats can be a risk to any business, organizations that have placed a temporary hold on security training may want to reconsider. For many businesses, using a training platform that sends out harmless, simulated phishing emails may be beneficial. Because emails sent out by the testing software are coded to identify those individuals that open and click within the message, organizational leaders can pinpoint vulnerable employees and provide further training to prevent a real attack.
What Makes for a Successful Pandemic Phishing Attack?
While the aforementioned threat of fraudulent Zoom invites is a textbook example of a “brand impersonation” scam, emails from Zoom aren’t the only messages individuals should keep a close eye on. In a study conducted by the security and data protection organization known as Barracuda, 2% of all phishing emails received in March of 2020 were COVID-19 related. Of that 2%, 34% were cybercriminal groups posing as reputable brands.
And although not all of those fraudulent emails resulted in successful hits for scammers, it remains clear that criminal groups are attempting to level heightened emotions around COVID-19 in an attempt to successfully distribute malware, steal credentials, and scam money. In turn both the FBI and the Federal Trade Commission have realized the severity of this issue, and have relayed strong warnings about phishing to the general public. Keeping that in mind, there are a few major categories of attack that business leaders and employees should remain hyper-aware of at this time.
Public Health Scams
As mentioned in the previously referenced article from Barracuda, many attackers are attempting to pose as authoritative figures. In particular, waves of emails have been hitting inboxes since early February, with hacking groups impersonating the Center of Disease Control, the World Health Organization, and other various medical organizations.
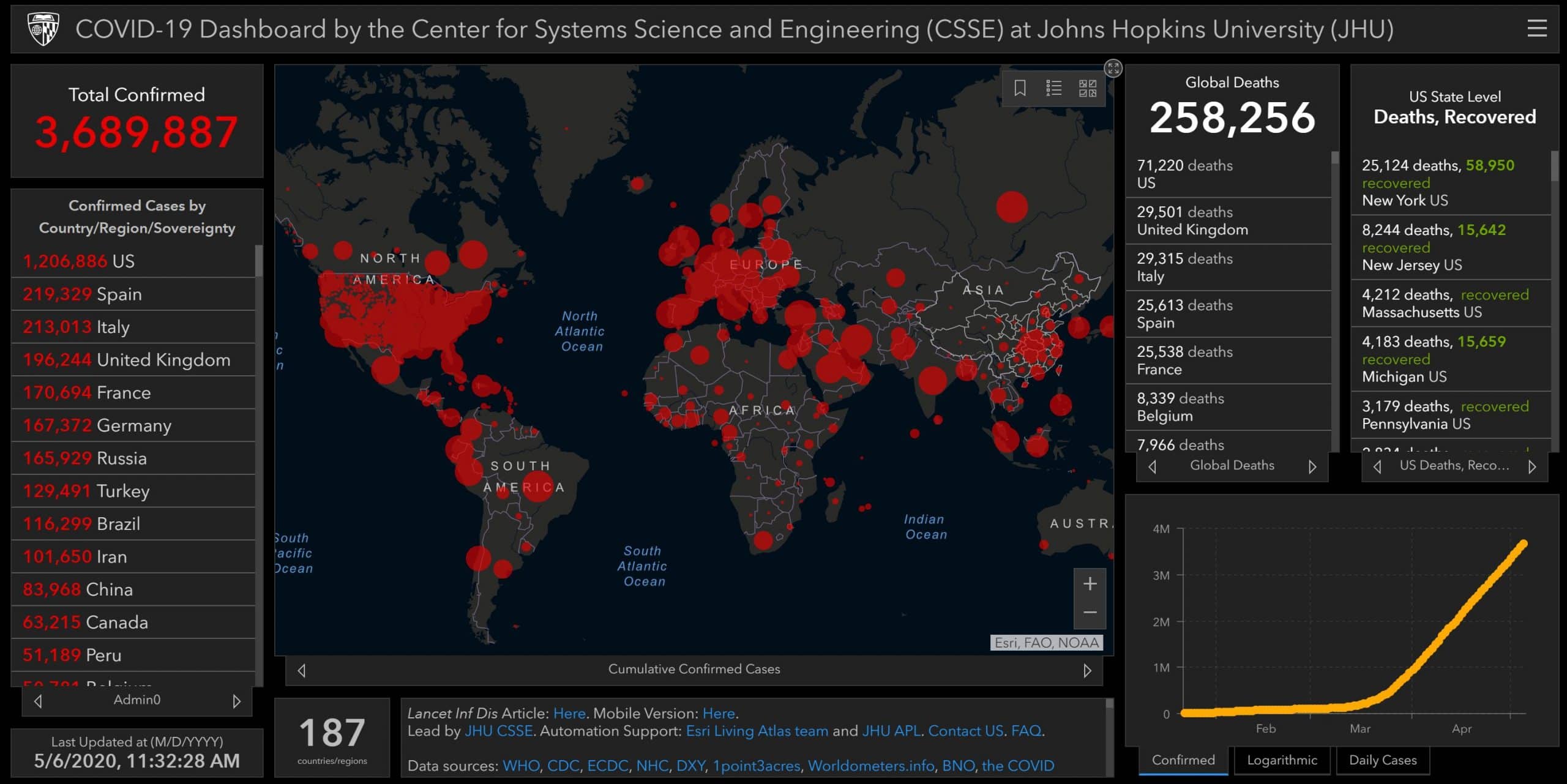
While the contents of these emails may vary, an interesting method that has been heavily adopted is the dispersion of fake coronavirus heat-maps. Using real time data and a very similar user interface to the one found on the authentic John Hopkins COVID-19 map, scammers are disguising malicious code as reputable information. As a result, when individuals click through to these fake sites, malicious code secretly begins to run in the background of the device.
Government Check Scams
Similar to public health scams, some hacking organizations are pretending to be financial government agencies, such as the IRS. In turn, these scammers ask individuals for either an application fee or personal information to access money that is owed to them. Most recently, this method of attack preys on those who are still waiting to receive stimulus checks in the mail or by direct deposit.
Business Email Scams
Likewise, businesses are also seeing commerce-based scams hit the inboxes of those in financial positions. As many may know, COVID-19 has caused quite the disruption in businesses that rely on face-to-face interaction. Because of this, many of these organizations have been forced to cancel deals, issue refunds, and shift to new electronic payment methods. Unfortunately, hackers see this as an opportunity to capitalize on any confusion, requesting refunds for large orders that may have never actually been placed.
Technology Scams
As one might note from the attempts criminals are making with fraudulent Zoom invites, technology-based scams are also a concern at this time. In addition to Zoom’s login page being spoofed, the Microsoft 365 and Outlook login pages are often recreated by scammers. But regardless of the page spoofed, attacks like this often only want one thing, and that’s to collect user login credentials. Once a criminal has this information, not only will they use it to log into the service it is associated with, they’ll also attempt to use it to break into other platforms that it may not be used for.
Therefore, it’s crucial that individuals use a different password for each site they visit; while also installing a password manager to easily and safely keep track of this information. For more details on the password managers recommended by Rocket IT, check out this article on password security.
Supply Scams
As the inventories of brick and mortar storefronts continue to be scarce, consumers have flocked to online marketplaces for essential items during the pandemic. Because of this, scammers have continued to distribute phishing emails, linking to fraudulent sites selling a list of items; ranging from face masks to toilet paper. In turn, not only will individuals that place an order with these sites not receive their order, it’s highly likely that their credit card information or identity will be captured and sold on the black market.
Charity Scams
Of all the phishing methods mentioned thus far, charity-based attacks are capable of leveraging emotions the most. Because many individuals are looking to help with relief efforts when possible, scammers are reaching out; posing as organizations seeking donations for COVID-19 victims, medical staff, or study funding. Additionally, some of these charitable emails may not be asking for money at all. Instead, criminals may be asking healthcare or other essential workers to provide identification to redeem fake promotions.
Policy Scams
As you can imagine, phishing isn’t a problem that begins and ends with this pandemic. As businesses adopt new policies for remote work, there are vulnerabilities that need to be taken into consideration. Already, scammers have begun to take advantage of people’s hopes to re-open the economy. In turn, scammers have begun spoofing emails to look as though they’re coming directly from an internal business leader, such as the CEO.
In these phishing emails, users are encouraged to click a link with a schedule of when the organization will reopen its door and return to normal operations. Once the link is clicked, typically one of two things happen. One, a user will be asked to enter Microsoft 365 credentials to gain access to the fake document, or two, malware will immediately be installed upon loading the page.
As mentioned before, scammers are known to engineer phishing emails that reflect the trending headlines of today. Keeping that in mind, not only is it important for employees to remain aware of these ever-changing phishing themes, it’s crucial that all team members understand the tell-tale signs that also change with these attacks.
To ensure employees remain up-to-date on this information, many businesses opt to routinely conduct the phishing testing procedure mentioned earlier. Doing so across an entire organization can help determine which individuals pose a risk to the business; while also allowing leaders to provide these individuals with security training before a successful attack occurs.
Although Rocket IT strongly suggests using formal security training to mitigate the long-term risks associated with phishing attacks, learning how to spot a fraudulent COVID-19 or Stimulus Check scam can provide individuals with foundational knowledge to build upon in the future. Aside from the standard rules of checking the legitimacy of a sender’s email and looking for grammatical errors in emails, here are a few best practices to remember when reading and responding to emails during the current pandemic.
IRS requests for an ID, upfront fee, or repayment of money: When it comes to applying for or checking on a stimulus check, the IRS will not ask that you email a copy of your identification to gain access to your money. In addition to not requesting a valid ID, the IRS will also not require an upfront fee to acquire more information on the status of your check. Keep in mind, there is no expedited process to receive a stimulus check, and reports have shown that checks will be mailed to those who don’t have direct deposit set up when filing taxes in early May. Finally, under no circumstance will the IRS imply that an individual was overpaid and demand that part of the stimulus package be returned.
Alerts for organizations claiming to track COVID-19 cases: Should an individual receive an email pertaining to the spread of COVID-19 from a major health organization, best practice is to assume that these emails are fraudulent. Instead of clicking a link within these emails, those interested in learning about the current state of the virus should visit either the John Hopkins, CDC, or WHO website.
Advice from medical experts: Similar to alerts from major health organizations, scammers are also sending emails posing as medical experts. Many times, these emails contain links or documents claiming to contain information on the steps needed to reduce the spread of the virus. Once again, Rocket IT suggests practicing extreme caution when opening such an email during the pandemic.
Ads that promote a sense of urgency to buy: As you might be able to tell, invoking a sense of urgency within phishing emails is a main tactic used by scammers. With that said, be aware that many cybercriminals are pushing non-existent cures or test-kits for COVID-19. As of now, the FDA has only approved the use of one home test, and it is extremely limited; requiring a doctor’s order to be obtained.
Urgent policy changes: As with any suspicious email from an individual you personally know, the best way to spot if a policy change is legitimate is to call the individual from which it apparently came and confirm its authenticity. For suspicious policy emails, this means employees should reach out to a manager or human resources manager with concerns.
Solicitation of charitable funds: Many charities understand that people are remaining cautious with their money at this time, so those organizations that reach out should be researched thoroughly to ensure their legitimacy. With that said, please note that legitimate charities will never ask individuals to mail cash, send gift cards, wire money, or purchase Bitcoin. Additionally, should the charity appear reputable, take extra precautions and find the organization via search engine; rather than clicking what could be a fraudulent link within the email received.
Preparing for Future Attacks
As mentioned multiple times in this article, research predicts that it’s only a matter of time before scammers once again alter their phishing tactics to realign with current world issues. Keeping that in mind, it’s important that employees within an organization understand that the simple click of an email can have both positive and negative impacts on the overall success of the business. In turn, it is every team member’s duty to remain updated on what to look for in phishing emails; bringing threats to the attention of the organization’s cybersecurity team. Doing so in a timely manner can protect sensitive information and ensure the doors of the business remain open during these difficult times.
To ensure team members know the key predictors of a phishing email, many phishing prevention systems, such as the one used by Rocket IT, can create harmless emails posing as an online meeting invitation, document sharing links, grocery delivery confirmations, shipping notifications, telemedicine offers, and business responses to COVID-19. By checking to see which individuals click on these emails sent through the training software, organizational leaders can pinpoint vulnerable employees and provide further training to prevent a real breach. For more information on Rocket IT’s phishing prevention system, please call 770-441-2520; or submit a request for more information using the contact form at the bottom of this page.



