Securing Office 365 With Microsoft Authenticator
Data breaches are no new area of discussion, but with the recent flood of incidents and the increased sophistication of cybercriminal attacks, what was once precautionary security measures have now become a necessity.
In Rocket IT’s previous account security series, the topic of multi-factor authentication (MFA) was front and center; presenting users with both a quick and highly effective method to protect their online assets. While this article isn’t going to delve too deep into the defining characteristics of MFA, the aforementioned article does a good job of summing up the core concept of MFA through the use of a simple analogy.
One Seamless Experience
Imagine, for a moment, that you’re patiently waiting in the TSA line at your local airport. Ticket in hand, you finally make it to the front of the line. But before crossing the barrier and dashing to your gate, you are suddenly halted by one of the airport’s agents. The agent politely asks to see some identification, comparing it to the information displayed on your ticket. Once the I.D. match is confirmed, you’re free to continue the boarding process and enter the facility.
Many login portals simply ask for a username and password (AKA your airline ticket), MFA requires the user to present a secondary piece of information to prove their identity and gain access to the account.
Noting the significant improvement this simple initiative can have on account security, many reputable developers have already begun to incorporate proprietary MFA software into their platforms; and Microsoft is no exception. While the PC development company has successfully published a few iterations of MFA applications in previous years, August 15, 2016, marked the date in which Microsoft merged its enterprise and consumer MFA offerings into one streamlined service: Microsoft Authenticator. More than just a new branding subsidiary, Microsoft’s updated merger between applications has brought about a variety of new benefits; such as push notifications, support for smartwatches, fingerprint approval, and certificate-based authentication. Now, while these features have proven to be a much-needed addition to the service, what really sets Microsoft Authenticator a step above the competition is its seamless incorporation into Microsoft Office 365 products; along with the control it gives to its enterprise administrators.
Through the use of Microsoft Authenticator, an organization’s administrator can enable and enforce MFA protocols across an entire team’s Microsoft applications; such as Outlook, Skype, OneDrive and more. In return, team members have no choice but to install the MFA software, greatly mitigating the chance of a company-wide breach occurring due to the human error of a single individual. That said, properly enabling MFA across an entire team can prove to be quite the project. Therefore, to cut the time and labor associated with such a task, many clients choose to enlist the help of Rocket IT’s technical staff. With the dedicated support of trained IT professionals, MFA policies can be launched across an entire company within a matter of hours. To learn more about this streamlined integration process, give Rocket IT a call at 770-441-2520, or fill out the form located at the bottom of this article.
That said, the speed in which MFA can be deployed across a business is dependent upon how educated the staff is on the application, its installation, and its use. Hence, in the remainder of this article, a step-by-step guide is presented to assist in the installation process; potentially alleviating some questions or concerns from the impacted end-users.
How to Install Microsoft Authenticator Across a Network
Step 1
As mentioned, a prerequisite of deploying MFA across an entire team of Office 365 users is that it is first enabled by the company’s administrator. Typically, this individual is one who has a solid understanding of enterprise networking, data management, and monitoring the effectiveness of security initiatives. Again, to begin this process, Rocket IT suggests contacting your internal IT professional.
Step 2
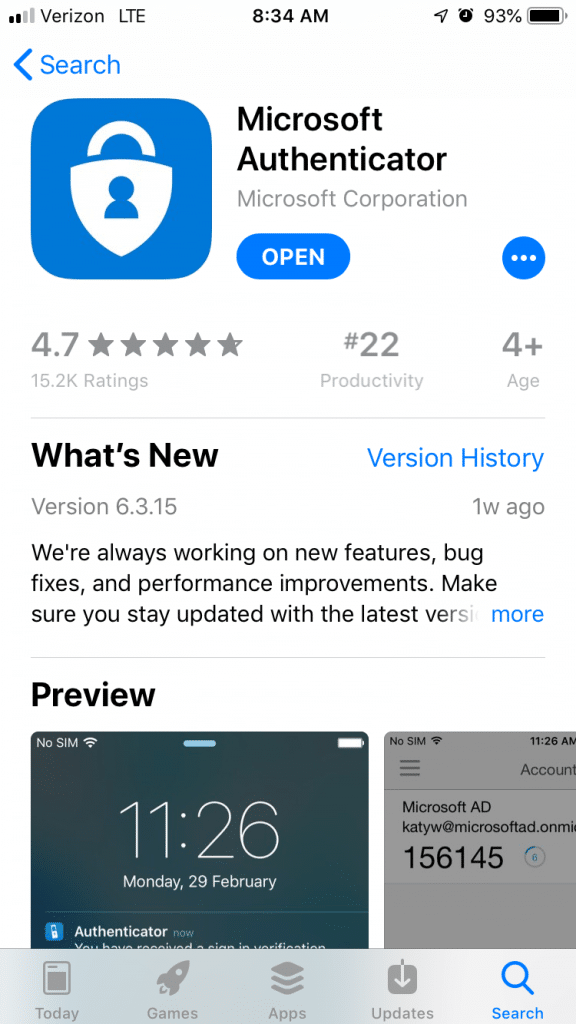
Via the Google Play or iOS App Store and download the Microsoft Authenticator app.
Step 3
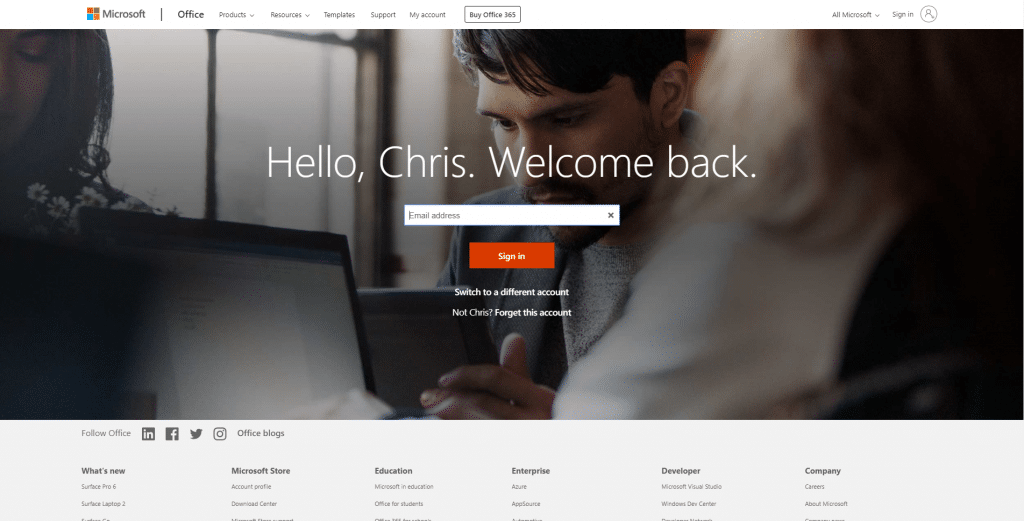
Next, on a desktop or laptop device, visit https://www.office.com. For users who already have an account, sign in as you would normally. Otherwise, speak to your organization’s admin about the proper steps to create an account on your business’s network.
Step 4
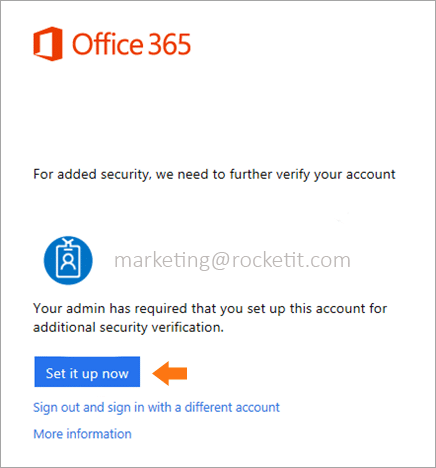
Upon signing in for the first time after MFA is enabled, users will be prompted with a popup to configure MFA for logging into Office.com. Click “Set it up now”.
Step 5
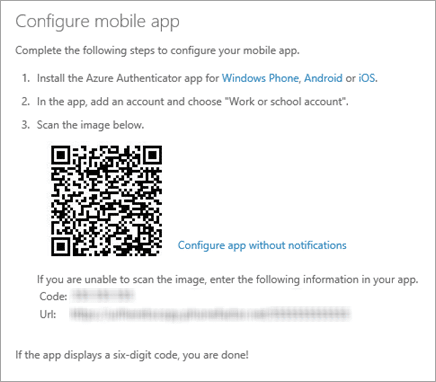
After the initial setup of your account, you will be greeted with a QR code. Using the Microsoft Authenticator app on your mobile device adds the account associated with your business. Once completed, use the app to scan the code displayed on your computer’s monitor.
Step 6
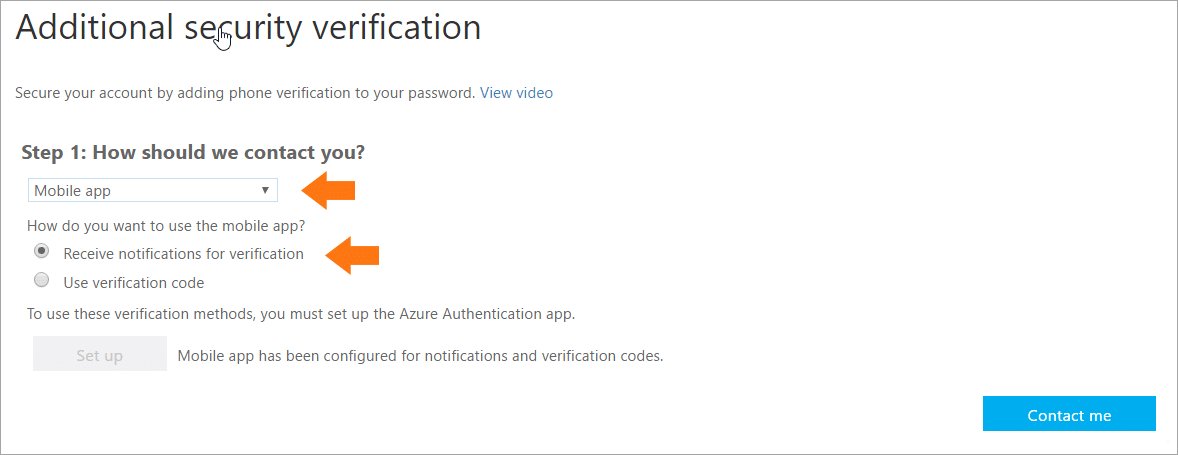
If done properly, the next prompt displayed on your computer monitor will ask how you’d like to be contacted. Select “Mobile app” from the drop-down menu and then check that you would like to receive notifications for verification. Look back to your mobile device and approve the sign-in prompt that is displayed inside of Microsoft Authenticator.
Step 7
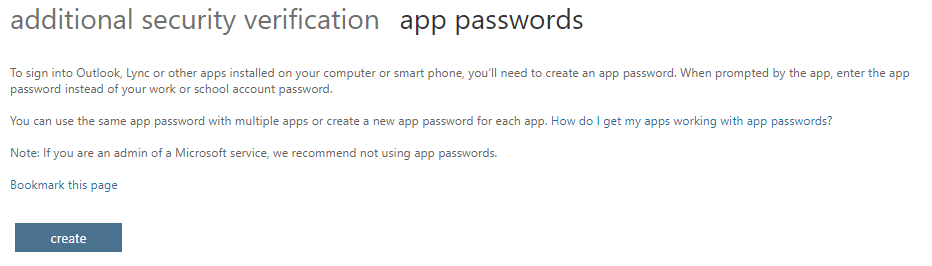
After continuing through the supplemental prompts Microsoft throws your way, visit https://account.activedirectory.windowsazure.com/AppPasswords.aspx. For authenticating Office 365 applications on your desktop device, a new master password needs to be created. After following the prompts from the website above, logging into Office 365 platforms for the first time after the password’s creation will require users to copy and paste this code into the login portal; instead of your normal credentials. That said, this system can be finicky on occasion, requiring new profiles to be created in the Control Panel of the user’s desktop. Once again, it is encouraged to have an IT professional on hand should an issue like this arise.
Mission Complete
After step seven is complete, a user is free to use their normal login credentials when attempting to access https://www.office.com. That said, before access to the user’s account is permitted, the individual will first need to approve a push notification via mobile device prior to gaining access to the account.
As a final word of caution, because this form of MFA relies on the use of a mobile device, it’s important that the organization’s administrator understand the proper backup protocols, should a user lose access to their mobile device. Once again, if you should have any questions or concerns about the implementation MFA across Office 365’s suite of products, contact Rocket IT at 770-441-2520, or by filling out the form below.
Related Posts
Subscribe to Rocket IT's Newsletter
Stay up to date on trending technology news and important updates.

Find out if Rocket IT is the right partner for your team
Claim a free consultation with a technology expert.










