Update Your Google Chrome Browser | New Zero-Day Vulnerability Alert
In light of two recently discovered security risks found within the Chrome Internet browser, Google engineers have begun distributing an important update across the platform’s entire user base. Known commonly as “zero-day vulnerabilities”, these potentially malicious threats were uncovered by two senior researchers at Kaspersky, a cybersecurity organization, on October 31, 2019.
What is a Zero-Day Vulnerability?
Zero-day vulnerability refers to a security flaw that is unknown by developers of a software, but could potentially pose a rather large risk to its users. Although the vulnerabilities discussed in this post pertain to Google Chrome, similar risks can lie in just about any type of software or platform. Because these vulnerabilities are difficult to find, teams of researchers spend hours upon hours of time scanning and documenting the back-end code of popular programs. In return, major developers of these platforms typically offer cash rewards to those researchers that both find the vulnerability and bring it to the attention of their team.
That said, if these vulnerabilities are not found and resolved quickly, the risk of exploitation increases. For reference, exploitation occurs between the time it takes for the vulnerability to be discovered and the resolving update that follows. During this window of time, hackers carefully craft codes to take advantage of the software’s flaws. Depending on the severity of the vulnerability, malicious code can be developed to gain remote access to a computer, escalate user privileges, and creep deeper into the now accessible network.
Now, in regards to the zero-day vulnerabilities that struck the Chrome browser, Google is hesitant to release a final confirmation of how many users were impacted by such exploitations. With that said, both members of Kaspersky and the United States Cybersecurity and Infrastructure Security Agency (CISA) have gathered their own information regarding these vulnerabilities, the potential reach of their exploitations, and the real dangers facing the average web user.
Identifying the Cause
In documentation presented by Kaspersky, two vulnerabilities were identified – one of which the Kaspersky team believes has been successfully used to gain access to one Chrome user’s computer.
For those individuals who are wondering how this event transpired, Kaspersky has confirmed that the exploit can be traced back to a Korean news website. Taking advantage of users with out-of-date versions of Google Chrome, attackers used the site as a tool to load a malicious third-party script onto the computers of unsuspecting users. Once secretly installed, the script would then check the current version of the user’s browser to ensure it contained the correct environment for the malware to take hold of the individual’s device.
Although Kaspersky’s team has only been able to confirm one known case of this exploit affecting a Chrome user’s computer, research continues to determine how far these attacks have been able to spread.
How to Protect Your Device
While it is important to be aware of vulnerabilities, such as this, the attention this event has produced will most definitely draw in other cyber criminals with like minded intentions. As a result, it is imperative for Chrome users to update their browsers with the newest patch Google has begun to roll out. Otherwise, the potential to be hacked still remains.
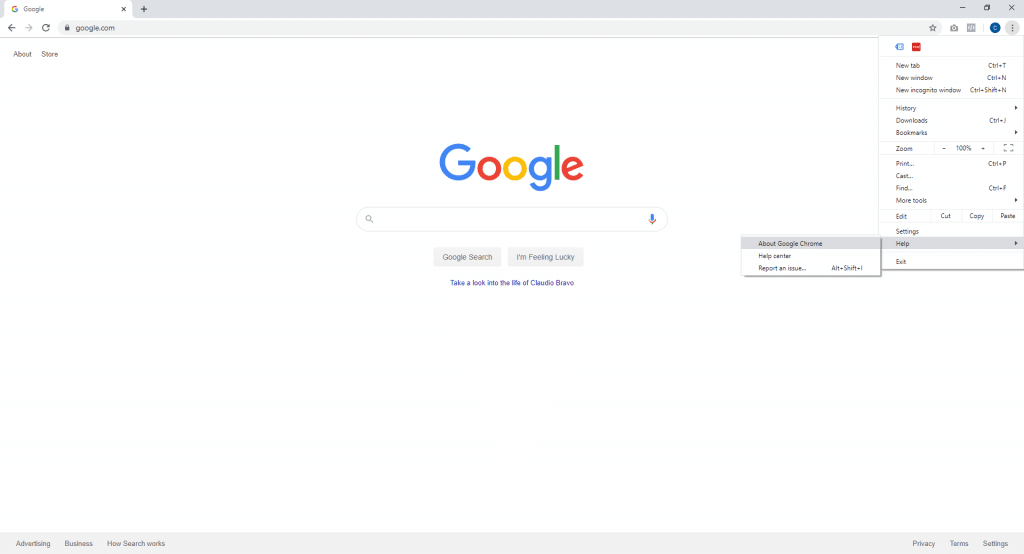
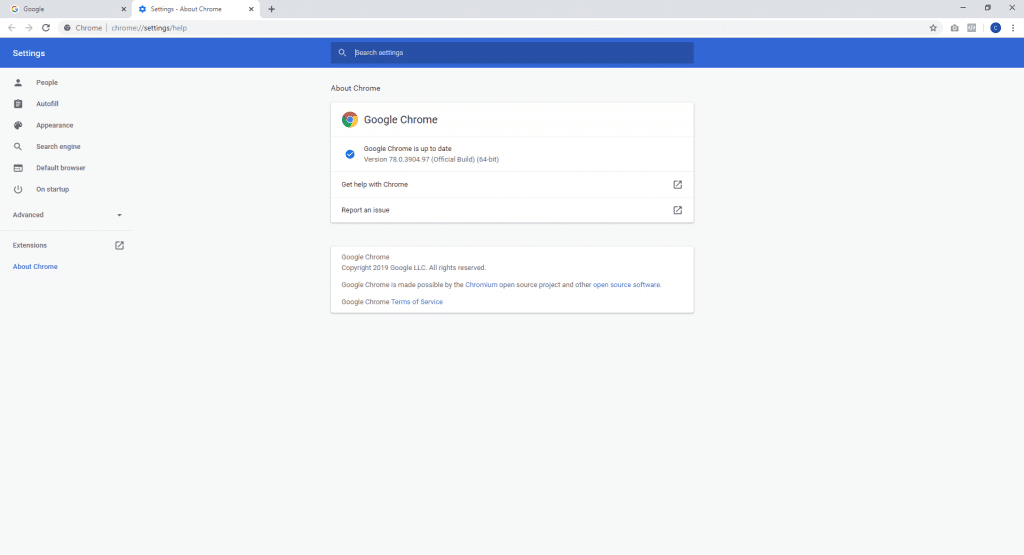
To complete this objective, open the Chrome browser and click the three vertical dots located in the top-right corner of the window. From the menu that appears, place the mouse pointer over the menu item labeled “Help” and select “About Google Chrome”. Here, users can check the current version of their browser, ensuring the most recent security updates have been installed. As of the time of this article’s writing, users should have their browsers updated to version 78.0.3904.87. If a number lower than this is seen in the About section of Chrome, follow the prior steps and click “Relaunch”.
It’s important to understand that vulnerabilities, such as these, are discovered on a regular basis. Just last March, Google faced an onslaught of open threats within Chrome. As a result, the organization was forced to quickly release a patch to resolve an eerily similar vulnerability to the one mentioned above. Now, with Google’s huge Chrome update and a range of new features having just recently released, security experts have now begun to complete a new wave of research.
Because of this, it’s important to have a team of technology-minded individuals on hand, capable of simplifying complex terms and concepts found in the research’s documentation. Fortunately, Rocket IT is here to help clients navigate through this clutter, helping them mitigate risks and decreasing the chance of productivity downtime. For more information on Rocket IT’s security offerings, give our team a call at 770-441-2520.
Related Posts
Subscribe to Rocket IT's Newsletter
Stay up to date on trending technology news and important updates.

Find out if Rocket IT is the right partner for your team
Claim a free consultation with a technology expert.










