Case Story | Enhanced Security – Manufacturing
Training employees on the tell-tale signs of a phishing email takes time—time you may not have now that you know more attacks occurred in the first six months of 2020 than all of 2019.
And although many businesses rely on traditional antivirus, firewalls, and spam filters to circumvent the vulnerabilities presented by such threats, one Rocket IT client quickly learned those measures alone are no match for an era of modern attacks.
You’re a Manufacturing Giant
For a moment, step into the shoes of one of Gwinnett County’s largest manufacturing fulfillment operations. Responsible for managing the software, inventory, and production for thousands of customers across the United States, a single attack could lead your business plummeting into a whirlwind of downtime and remediation costs.

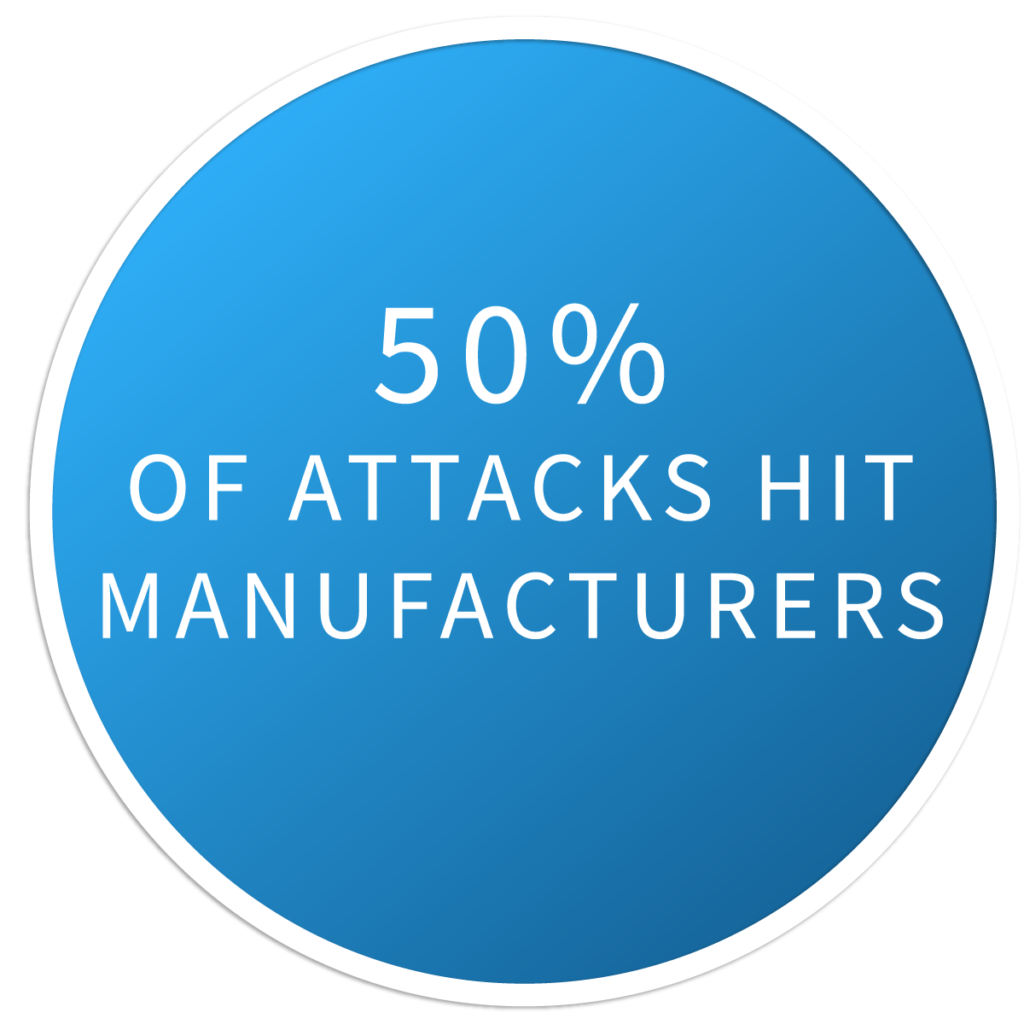
You’re a High-Value Target
Recently hearing that 50% of organizations affected by cyber attacks in 2019 are in the manufacturing sector, you take this as a warning sign that basic security may not be enough to protect your multi-million dollar operation. You begin to search for an enhanced solution capable of providing higher visibility, greater surveillance, and faster response times when malware is detected. But with the company’s most profitable months quickly approaching, time is ticking.
You Contact Rocket IT For Help
Within 24 hours of hearing these concerns, Rocket IT’s team of cybersecurity experts evaluate your current security environment and strategized a plan to deploy endpoint detection and response (EDR) and application whitelisting software across your entire network of users.

Over the Next Few Days…
Once successfully installed, the first alert rolls in, notifying Rocket IT engineers of an individual’s attempt to visit a malicious site. Although the new technologies work in unison to prevent malware from secretly installing and stealing login credentials, a password reset is required to preserve the individual’s account security. A Rocket IT technician immediately reaches out to the victim to assist with the process. While the technician waits to confirm login credentials have been changed, the individual’s access to sensitive data is revoked, mitigating the malware’s spread to other devices.
Over the next few days, additional surveillance alerts are triggered. By following what is essentially a trail of digital breadcrumbs, Rocket IT engineers trace the alerts back to a PC that was compromised prior to the deployment of Rocket IT’s Enhanced Security offering. Upon this discovery, the compromised computer is pulled offline and transported to Rocket IT’s headquarters for deep cleaning. After the threat is removed, the device is transported back to your office where its connection is restored.
In the coming days, no additional alerts transpire, confirming the network has been successfully cleaned.
Remaining Ahead of the Curve
EDR and application whitelisting are quickly becoming industry standards, with 86% of IT companies already deploying some form of EDR on client networks and another 11% planning to invest in the next 12 months.
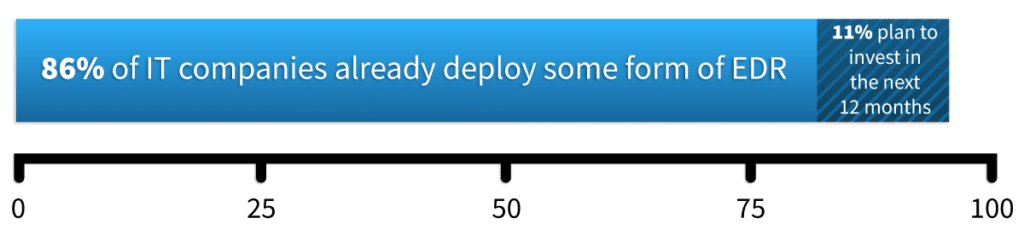
Mentioned previously, this rapid adoption of new technology can be attributed to the advancement of threats and a responsibility to keep clients up to date with modern cybersecurity trends.
“Traditional antivirus software tracks and blocks known viruses based on their unique signatures,” said Rocket IT Service Manager, Patrick Richardt. “Because new malware is developed daily, antivirus can’t keep up and it’s not uncommon for zero-day attacks to go unnoticed for extended periods of time on networks with outdated security.”
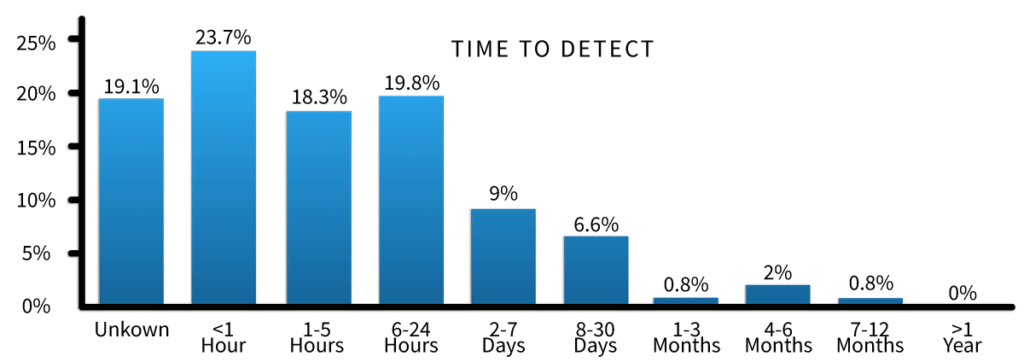
By adopting these technologies, advantageous businesses are able to identify and prevent 62% of threats within the first 24 hours rather than relying on traditional methods of security that may take days or weeks to disclose potential damages.
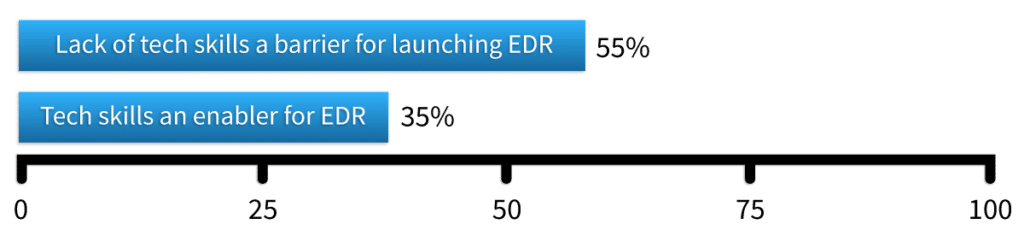
So, what’s stopping your organization from getting ahead of the curve? Unlike 55% of businesses lacking the skills to operate these advanced security measures, you have a team of highly trained engineers ready to help you take the next step.
Related Posts
Subscribe to Rocket IT's Newsletter
Stay up to date on trending technology news and important updates.

Find out if Rocket IT is the right partner for your team
Claim a free consultation with a technology expert.










